
Rawpixel - Fotolia
How do I design and initiate a call tree procedure?
A call tree can be an important piece of disaster recovery planning. Follow these steps for call tree design and execution to ensure your company is ready for unplanned events.
A call tree, sometimes referred to as a phone tree, can be a good way for an organization to notify specific individuals of a typically unplanned event and coordinate recovery, if necessary.
Before implementing any call tree procedure, you should have management buy-in.
Coordinate data-gathering activities with human resources, as that department will supply you with contact information. You also need to work with the emergency management team when developing the list of contacts and notification sequence. For example, should each person contact two people or three? Once you have decided on the calling process, have it reviewed and approved by your emergency management team.
Designing a call tree
The next step is to design the call tree and decide how many layers it will have. Contacting people should be easily accomplished, so employee information should include an office phone number, a cellphone number and an email address. Once the call tree structure and all contact data have been assembled, it should be submitted to the emergency team for review and then to management for final approval.
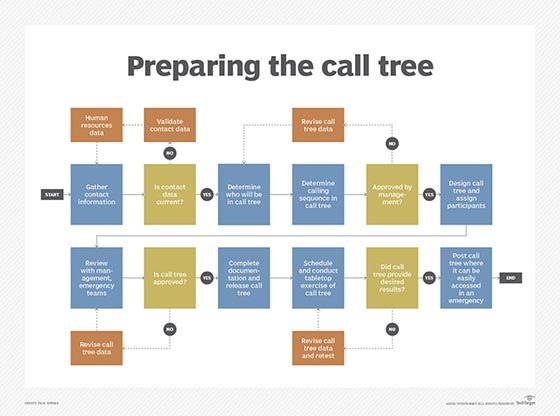
The emergency management team and other designated employees should then perform a walk-through of the call tree procedure to make sure everyone knows what to do in case of an emergency. Once the exercise has been completed and any updates have been noted, the call tree procedure should be posted in as many locations and formats -- such as print, company intranet and off-site storage -- as possible so it will be easy to access in an emergency.
Executing your call tree
Once the emergency management team -- or damage assessment team, if you have one -- has assessed the active incident and determined that employees must be notified, they can initiate the call tree.
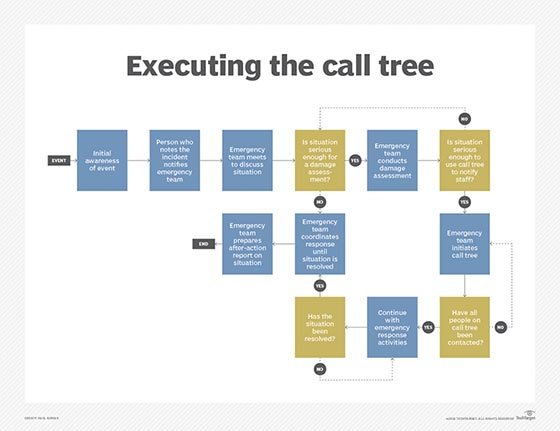
Secure the call tree procedure data from a convenient repository and begin making calls or sending messages. Call tree members should note which employees they were unable to contact, as that data must be relayed back to the emergency team for follow-up. Once everyone has been notified, proceed with emergency response plan procedures or move ahead with a business continuity plan, if needed.








